Welcome back to Messier Monday! Today, we continue in our tribute to our dear friend, Tammy Plotner, by looking at the barred spiral galaxy, Messier 58.
In the 18th century, while searching the night sky for comets, French astronomer Charles Messier kept noting the presence of fixed, diffuse objects in the night sky. In time, he would come to compile a list of approximately 100 of these objects, with the purpose of making sure that astronomers did not mistake them for comets. However, this list – known as the Messier Catalog – would go on to serve a more important function, becoming one of the first catalogs of Deep Sky Objects.
One of these objects is the intermediate barred spiral galaxy known as Messier 58, which is located approximately 68 million light years away in the Virgo constellation. In addition to being one of just four barred spiral galaxies in the Messier Catalog, it is also one of the brightest galaxies in the Virgo Supercluster. Due to its proximity in the sky to other objects in the Virgo Galaxy Field, it can be seen only with the help of a telescope or a pair of large binoculars.
Description:
This beautiful old barred spiral galaxy located approximately 68 million light-years from Earth. Although it might appear pretty plain, it has some great things going for it… namely an active galactic nucleus. As Marcella Contini indicated in a 2004 study:
“We have modelled the low-luminosity active galactic nuclei (AGN) NGC 4579 by explaining both the continuum and the line spectra observed with different apertures. It was found that the nuclear emission is dominated by an AGN such that the flux from the active centre (AC) is relatively low compared with that of the narrow emission-line region (NLR) of Seyfert galaxies. However, the contribution of a young starburst cannot be neglected, as well as that of shock-dominated clouds with velocities of 100, 300 and 500kms-1. A small contribution from an older starburst with an age of 4.5 Myr, probably located in the external nuclear region, is also found. HII regions appear in the extended regions, where radiation and shock-dominated clouds prevail.
“The continuum SED of NGC 4579 is characterized by the strong flux from an old stellar population. Emissions in the radio range show synchrotron radiation from the base of the jet outflowing from the accretion disc within 0.1 pc from the active centre. Radio emission within intermediate distances is explained by the bremsstrahlung from gas downstream of low-velocity shocks reached by a relatively low radiation flux from the AC. In extended regions the radio emission is synchrotron radiation created by the Fermi mechanism at the shock front. The shocks are created by collision of clouds with the jet. All types of emissions observed at different radius from the centre can be reconciled with the presence of the jet.”

Yet where is this gas traveling to and why? According to 2014 study by S. Garcia-Burillo (et al):
“We created a complete gravity torque map of the disk of the LINER/Seyfert 1.9 galaxy NGC 4579. We quantify the efficiency of angular momentum transport and search for signatures of secular evolution in the fueling process from r ~ 15 kpc down to the inner r ~ 50 pc around the active galactic nucleus (AGN). The derived gravity torque budget in NGC 4579 shows that inward gas flow is occurring on different spatial scales in the disk. In the outer disk, the decoupling of the spiral allows the gas to efficiently populate the UHR region, and thus produce net gas inflow on intermediate scales. The co rotation barrier seems to be overcome by secular evolution processes. The gas in the inner disk is efficiently funneled by gravity torques down to r ~ 300 pc. Closer to the AGN, gas feels negative torques due to the combined action of the large-scale bar and the inner oval. The two m=2 modes act in concert to produce net gas inflow down to r ~ 50 pc, providing clear smoking gun evidence of inward gas transport on short dynamical timescales.”
What causes inward transport of gases? Why, a massive gravity pull of course. And what could be more gravitational attractive than a black hole! As Eliot Quataert (et al) indicated in their 1999 study:
“M81 and NGC 4579 are two of the few low-luminosity active galactic nuclei which have an estimated mass for the central black hole, detected hard X-ray emission, and detected optical/UV emission. In contrast to the canonical “big blue bump,” both have optical/UV spectra which decrease with increasing frequency in a plot. Barring significant reddening by dust and/or large errors in the black hole mass estimates, the optical/UV spectra of these systems require that the inner edge of a geometrically thin, optically thick, accretion disk lies at roughly 100 Schwarzschild radii. The observed X-ray radiation can be explained by an optically thin, two temperature, advection-dominated accretion flow at smaller radii.”
Galaxy NGC 4579 was captured by the Spitzer Infrared Nearby Galaxy Survey (SINGS) Legacy Project using the Spitzer Space Telescope’s Infrared Array Camera (IRAC). In this image, the red structures are areas where gas and dust are thought to be forming new stars, while the blue light comes from mature stars. This SINGS image is a four-channel, false-color composite, where blue indicates emission at 3.6 microns, green corresponds to 4.5 microns, and red to 5.8 and 8.0 microns. The contribution from starlight (measured at 3.6 microns) in this picture has been subtracted from the 5.8 and 8 micron images to enhance the visibility of the dust features.

History of Observation:
When Charles Messier discovered this one on April 15, 1779, I’m sure he didn’t know he was looking back into time when he wrote:
“Very faint nebula discovered in Virgo, almost on the same parallel as Epsilon, 3rd mag. The slightest light for illuminating the micrometer wires makes it disappear. M. Messier reported it on the chart of the Comet of 1779, which is located in the volume of the Academy for the same year.”
Messier 58 may not have been a comet, but it certainly was another distant cousin of our own Milky Way!
Locating Messier 58:
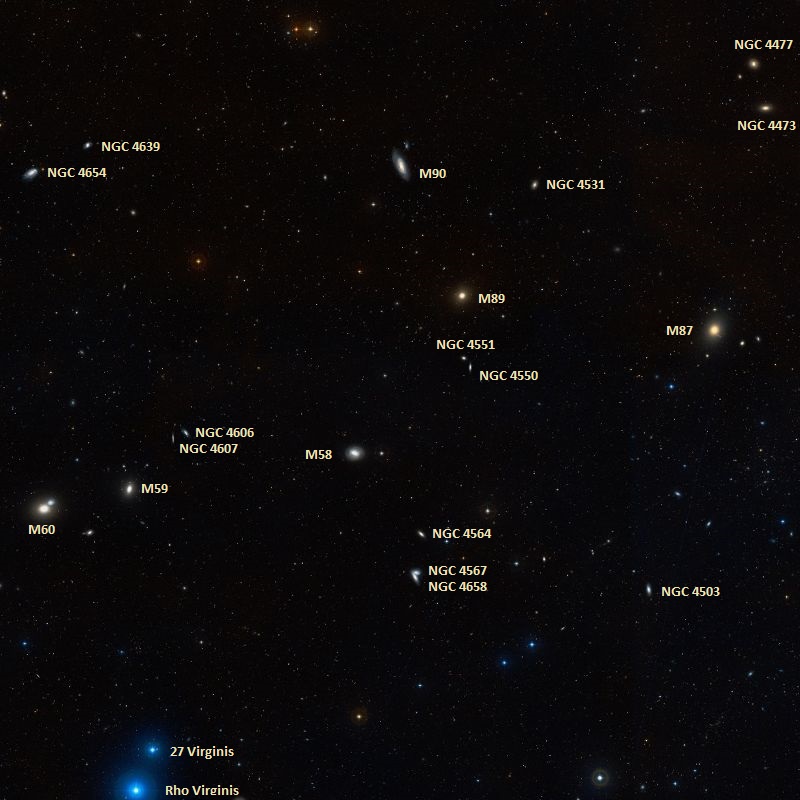
Finding M58 requires a telescope or large binoculars, and lots of patience. Because the Virgo Galaxy field contains so many galaxies which can easily be misidentified, it is sometimes easier to “hop” from one galaxy to the next! In this case, we need to start by locating bright Vindemiatrix (Epsilon Virginis) almost due east of Denebola. Let’s hop four and a half degrees west and a shade north of Epsilon to locate one of the largest elliptical galaxies presently known – M60.
At a little brighter than magnitude 9, this galaxy could be spotted with binoculars, but stick with your telescope. In the same low power field (depending on aperture size) you may also note faint NGC 4647 which only appears to be interacting with M60. Also in the field to the west (the direction of drift) is our next Messier, bright cored elliptical M59. Now we will need to continue about an average eyepiece field of view, or a degree further west of this group to bring you to our “galactic twin”, fainter M58.
In a smaller telescope, do not expect to see much. What will appear at low power is a tiny egg-shaped patch of contrast change. As aperture increases, so does detail and a bright nucleus will begin to appear as you move into the 4-6″ size range and dark sky locations. As with all galaxies, dark skies are a must!
And here are the quick facts on this object to help you get started:
Object Name: Messier 58
Alternative Designations: M58, NGC 4579
Object Type: SBc Galaxy
Constellation: Virgo
Right Ascension: 12 : 37.7 (h:m)
Declination: +11 : 49 (deg:m)
Distance: 60000 (kly)
Visual Brightness: 9.7 (mag)
Apparent Dimension: 5.5×4.5 (arc min)
We have written many interesting articles about Messier Objects here at Universe Today. Here’s Tammy Plotner’s Introduction to the Messier Objects, M1 – The Crab Nebula, and David Dickison’s articles on the 2013 and 2014 Messier Marathons.
Be to sure to check out our complete Messier Catalog. And for more information, check out the SEDS Messier Database.
Sources: